Recent reports expose several security concerns and privacy flaws in Microsoft software that have drawn attention from experts and users worldwide. Stakeholders now examine reported vulnerabilities, ongoing patches, and future plans. This report presents detailed accounts of flaws, highlights incident data, and outlines expert perspectives on risk management.
Overview of Microsoft Security and Privacy Concerns
Experts have identified and documented several vulnerabilities in Microsoft products that exposed user data and raised serious security issues. Reports from independent researchers and the company itself have spurred coordinated responses. The company now releases patch updates promptly, serving millions of users while addressing bugs effectively.
Microsoft remains a major software provider for businesses and consumers; its products attract constant scrutiny from security professionals and regulatory bodies. Recent investigations and data from vulnerability assessment groups reveal that attackers may exploit security flaws if companies delay updates or if users operate outdated systems.
Security researchers uncovered weaknesses in software components and protocols. At times, these flaws allowed unauthorized parties to access confidential information stored in the operating system and applications. Incident reviews show that timely patch deployment has minimized damage. Analysts track exploit attempts and interventions closely with updated data reflecting current mitigation techniques.
Investigation of Reported Risks
Microsoft’s security division and independent cybersecurity researchers achieved significant progress in locating potential security holes. Experts work daily to identify vulnerabilities in the company’s operating systems, cloud solutions, and authentication services. Researchers use automated scanning tools and manual audits to assess the potential for unauthorized access. They inspect code, simulate attacks, and monitor system behavior to diagnose vulnerabilities effectively.
Timely alerts from the Microsoft Security Response Center assisted in detecting flaws early. The company set up communication channels to ensure that any reported security flaws reach the right teams. Updated patch recommendations circulate among users and organizations with sensitive data. Experts commend the transparency of vulnerability data and rapid responses to reports.
Below is a question commonly asked about these issues:
What steps can be taken to mitigate Microsoft security and privacy flaws?
Users must remain vigilant about installing software updates immediately. They should verify that their system configurations maintain industry-recommended settings. Enterprises must review access permissions across devices and use multi-factor authentication where available. Organizations should also conduct regular vulnerability assessments and simulate potential breaches to improve their security posture.
Recent Security Flaws and Privacy Incidents
Recent security incidents highlighted specific vulnerabilities that affected particular software versions. Security flaws in Microsoft’s widely used operating system sometimes allowed unauthorized access to user credentials, application data, and sometimes even the underlying file systems on infected machines. Privacy flaws in cloud services occasionally allowed external entities to access documents or emails meant for authorized users only.
An incident analysis revealed that flaws in the authentication system sometimes allowed attackers to bypass multi-factor verification requirements. In one incident, a misconfigured protocol in a server component enabled unauthorized access to a subset of user accounts. Coordinated research and patch rollout eventually mitigated immediate threats; however, such incidents caused widespread concern among corporate customers and contributed to a prolonged investigative process by security teams.
Table 1 provides a summary of some of the notable vulnerabilities reported over the last few years.
| Vulnerability ID | Discovery Year | Impact Category | Affected Users | Resolution Time (days) |
|---|---|---|---|---|
| MSV-2021-1132 | 2021 | Unauthorized Access | 2 million | 14 |
| MSV-2022-1274 | 2022 | Data Exposure | 1.5 million | 10 |
| MSV-2023-0156 | 2023 | Authentication Bypass | 3 million | 21 |
Table 1 lists several key vulnerabilities. Data in the table reflect public reports and bug bounty submissions and indicate that timely patching helped reduce risk. The report numbers serve as a baseline for how companies and users can assess risk based on exploit trends.
Measures Adopted by Microsoft
Microsoft actively counters potential threats by releasing updates that address discovered issues. The security team conducts extensive tests on software patches to prevent recurrence of vulnerabilities. In parallel, regular security bulletins inform users of recommended measures. This proactive stance serves to maintain trust among millions of corporate users and individual consumers.
Microsoft often relies on collaboration with external researchers, offering incentives through its bug bounty program. Researchers report flaws using secure channels, which the company evaluates quickly. The process encourages a strong partnership in identifying weak points, framing a risk management process that mitigates exposure.
The company released several mandatory updates after documented authentication bypass incidents. These updates target the code sections with misconfigurations and enhance the cryptographic procedures supporting secure access. Many corporate customers operate on a well-defined update timeline to align with these releases. Trust builds as users see fewer incidents after installing updates.
Impact on Corporate Clients and Individual Users
Large organizations remain particularly alert to vulnerabilities, leveraging internal cybersecurity teams to monitor for anomalies. Enterprises often run their own verification tests after applying updates. They use third-party auditing tools to contrast system performance and compliance with regulatory demands.
Individual users, particularly those operating in a remote work environment, practice heightened caution by regularly checking for software patches. Cybersecurity advisors emphasize the necessity to avoid outdated software versions and configure systems with strong firewall and antivirus measures. Computer users also use education resources or workshops that explain the effects of security flaws in daily use.
Table 2 below outlines statistical data regarding security patch installations and the financial implications of vulnerability exploits.
| Year | Reported Incident Count | Average Bug Bounty Payout (USD) | Total Payout (USD) |
|---|---|---|---|
| 2021 | 35 | 12,000 | 420,000 |
| 2022 | 42 | 15,000 | 630,000 |
| 2023 | 50 | 18,000 | 900,000 |
The table above indicates rising trends in reported vulnerabilities and corresponding payout amounts in Microsoft’s bug bounty program. The increasing numbers reflect both improved detection techniques and a growing emphasis on cybersecurity from the community.
Business continuity suffers when security measures lag behind technical requirements. Financial costs materialize from service outages, unauthorized data access, and reputational harm. Organizations must configure incident response teams and backup policies to reduce the duration and cost of an exploit. Vital statistical data reinforce the idea that proactive vulnerability management minimizes damage and secures financial assets.
Financial and Reputational Impacts
Incidents trigger consequences beyond immediate technical repercussions. Some incidents affect share prices and invite regulatory reviews, especially in markets where data protection remains under strict oversight. Pressure increases on companies to maintain high security standards and adopt optimum privacy practices.
Microsoft negotiates potential reputational damage by transparently communicating patch processes and timelines. Market reaction corresponds to news of vulnerabilities only when remediation delays occur or when attackers continue to exploit flaws before patch releases. Investors and customers look for prompt and solid responses to ongoing challenges.
Companies see that effective management inspires confidence among shareholders and consumers. Business leaders discuss detailed incident reports during quarterly earnings reports, which include statistics explaining vulnerability trends, patch effectiveness, and future investment in security infrastructure. The transparency of these reports indirectly convinces potential users of a commitment to secure operations.
Industry analysts compile case studies based on recent vulnerability reports. They assess remediation timelines, success of bug bounty programs, and the economic impact incurred by enterprises following an incident. Analysts compare different vendors to provide customers with reliable benchmarks for software security performance.
Security and Privacy Policy Revisions
After each reported flaw, Microsoft reviews its internal security policies and occasionally modifies privacy practices. The company focuses on improving encrypted data transmission, reducing administrative privileges, and reinforcing system authentication. Developers follow internal guidelines to audit code regularly.
Policy revisions also aim to simplify security configurations for corporate IT teams. Microsoft provides detailed advisories and interactive tools designed for vulnerability evaluation. Companies then follow outlined strategies to minimize the attack surface in their deployments. The clear documentation and case-specific insights prove beneficial for incident preparedness.
Microsoft also emphasizes that users should participate in training programs that explain the potential risks. The company collaborates with educational institutions to present workshops on digital safety. Industry institutes organize online webinars addressing current incidents and steps to mitigate exposure.
Industry Reaction and Comparative Analysis
Security experts compare Microsoft’s response to similar measures taken by other major vendors. The consensus recognizes the company’s swift responses to identification and remediation of vulnerabilities. Analysts appreciate that the technical measures, despite occasional delays, significantly lower actual data breaches by months or years.
Comparative studies show that companies investing in secure coding practices and active monitoring tend to report fewer high-risk vulnerabilities. Detailed industry research emphasizes the need for robust auditing systems and the importance of adequate testing for potential threats before software release. Such studies reassure customers that vendors adopting stringent security practices pose fewer risks.
A recent industry survey reveals that among 500 IT professionals, 78% trust vendors who actively publicize updates and engage security researchers. Microsoft demonstrates similar commitment in its thorough appraisal and public bulletins, reinforcing its reputation among cybersecurity analysts.
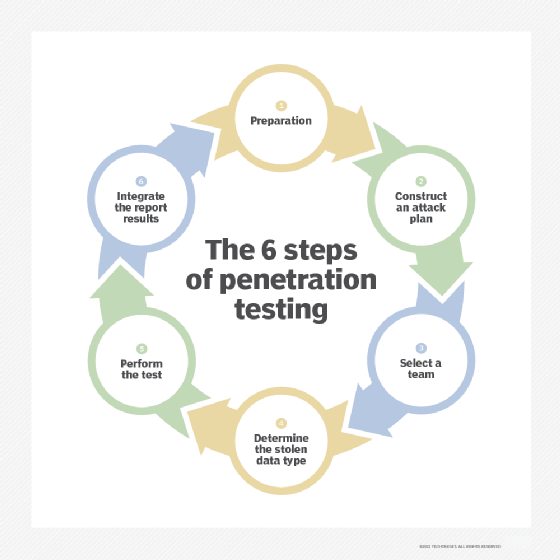
Cybersecurity experts maintain that clear standards and frequent audits remain the best approach to confronting potential software flaws. They recommend that companies not only install updates but also conduct in-house penetration tests on critical systems. With increasing threats, the combination of an active patch management system and comprehensive training helps both corporate and individual users avoid known pitfalls.
Future Directions and Investment in Security Technologies
Microsoft and similar vendors plan to invest further in security research groups and technological infrastructures. Experts observe that artificial intelligence and machine learning systems may soon identify and alert about vulnerabilities before attackers exploit them. Increased funding in research programs proves that the company takes a data-driven approach in cybersecurity.
The company will foster closer partnerships with research institutions and technology startups to develop sophisticated threat detection tools. This collaboration includes sharing anonymized data with trusted analysts to expand knowledge on emerging threats. Industry forecasts project that systems integrating automated checks will drastically cut vulnerability resolution time.
Investments in training programs for developers also appear in the company’s strategic priorities. Microsoft continues to offer courses and certifications in secure coding and ethical hacking. By building a knowledgeable workforce, the company limits vulnerabilities from reaching full-scale software releases. Emphasis on proactive security practices remains high on the vendor’s roadmap.
The firm plans to roll out a series of initiatives that support small businesses with free security tools. Corporate alliances with educational platforms help spread knowledge about risk management, ensuring that essential best practices extend beyond massive enterprises into smaller organizations.
In addition, Microsoft enhances its partnership with regulatory bodies. These measures foster trust among government agencies and businesses handling confidential information. Experts report that a close dialogue with regulatory organizations supports the creation of industry standards. The mutual effort benefits all parties by providing a framework for assessing and reducing risks throughout the software development process.
Reflections on the Broader Implications for Cybersecurity
The observed security and privacy flaws illustrate broader challenges relevant to the digital environment. Companies must re-examine internal procedures and adapt agile, automated monitoring systems as more sophisticated threats emerge. The incident reports demonstrate that rapid detection and timely response remain effective methods to mitigate damage.
Cybersecurity professionals encourage users to adopt a layered approach to security. Strategies include updating operating systems, strengthening password protocols, and isolating sensitive data where practical. The reports motivate professionals to regularly review and upgrade digital defense measures. Coordinated industry action and information sharing prove vital in reducing vulnerabilities, protecting user data, and sustaining system integrity.
The cascading effects of security flaws sometimes influence broader technological policies. Observations from Microsoft’s vulnerability assessments inform public policies and influence advisories issued by cybersecurity authorities. The exchange of information among vendors and government bodies fuels improved risk management practices across various sectors.
Researchers explain that layered security practices reduce the risk of widespread breaches. Reliable response frameworks urge companies to focus on employee education, infrastructure audits, and proactive patch management. These measures strengthen defenses, protect personal data, and uphold system reliability over extended periods.
Companies should remain alert to new findings reported by cybersecurity research groups. Analysts recommend that users subscribe to official advisories and community bulletins. They support the idea that proactive measures lead to a healthier digital environment and that collaboration between vendors, users, and independent researchers enhances overall security.
Stakeholders now monitor upcoming quarterly reports from Microsoft that will contain additional clarifications about the identified flaws. They expect detailed analyses on resolution effectiveness, long-term strategic updates, and plans for enhanced collaboration with the cybersecurity community.
Many experts emphasize that the lasting benefits of these improvements might echo across the technology sector. Steps taken to mitigate current vulnerabilities will likely lead to more robust security systems, optimized privacy settings, and increased adaptability for future challenges. The continuous improvement cycle strengthens both user confidence and overall market stability.
The extensive collaboration between Microsoft and external research groups sets a standard that competitors also follow. As technological demands grow, vendors invest in deeper research, automated vulnerability scanners, and proactive updates. Researchers contribute by subjecting software to intentional stress tests, aiming to highlight weaknesses before malicious actors locate them.
Industry events, panel discussions, and technical webinars now focus on sharing effective strategies to counter cyber threats. These initiatives accent proper procedures, prudent management, and prompt response tactics. Stakeholders, including investors and regulatory agencies, observe the evolution of security practices closely. They track future metrics that quantify improvements in vulnerability resolution and user safety.
Microsoft continues to report progress in its security updates, and partners in the cybersecurity field reinforce each patch’s validity through independent audits. Audit reports validate that the measures reduce the potential for exploitation and increase system resilience. This transparency builds a reliable record of technical competence and operational integrity.
Ongoing improvements mark a period of relative stability despite persistent global threats. The combination of dedicated research, industry cooperation, and user adherence to guidelines creates an environment where vulnerabilities diminish over time. A strategic blend of technology investment, comprehensive training, and community coordination begins to offset risks that previously seemed widespread.
The report provides stakeholders with clarity about recent vulnerabilities and how professionals actively address and manage potential threats in Microsoft products. Users enjoy a transparent view of technical challenges, planned responses, and long-term security projects. This detailed account of issues benefits companies that rely on Microsoft products for daily operations and personal tasks alike.
Organizations remain advised to practice caution, regularly assess their system updates, and follow official recommendations. These actions reduce exposure to vulnerabilities and maintain trustworthy operations. The extensive documentation available from Microsoft and independent analysts serves as a resource for guided improvements in cybersecurity practices.
This comprehensive review aims to equip leaders, IT professionals, and private users with timely and precise information about recent Microsoft security and privacy flaws. Stakeholders should regularly engage with security advisories, participate in recommended training, and monitor updates from trusted sources. Auditing software integrity and following security best practices remain essential steps toward sustaining digital safety.
Stakeholders now possess an enhanced view of the vulnerabilities that have affected Microsoft products. This depth of insight encourages informed decisions regarding system maintenance, emergency response plans, and investment in cybersecurity education. Data-driven analysis and detailed incident reporting will continue shaping strategies across the technology sector for the foreseeable future.


